Author Marko Krstic
How to use public wifi safely? (DO THIS)
It's hard to imagine life nowadays without the internet. We use it for many different reasons almost every day. Whether just reading the news, browsing interesting magazines, checking emails, or purchasing online, we always need a good internet connection.
It's not rare that we use the internet in public areas, such as restaurants, hotels, train stations, etc. We often ask our host in the restaurant for internet credentials, and there we go, we are connected.
But being connected to the internet via public wifi takes a specific risk. Many people are not aware of what might happen and how to prevent it. We will try to explain how to stay safe using public wifi.
How it works
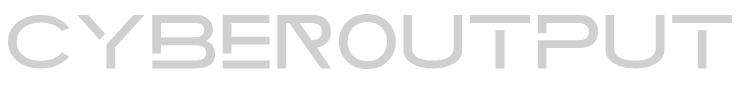
Before explaining the risks, let's first look at what happens when we connect to the internet. We will present a simplified version of what happens when we start, let's say, logging into Facebook over public wifi in a restaurant.
We will also explain the vocabulary around networking (http request, http response, server, client, router etc.)
From the picture above, we can see that we have to connect to the internet first to access a Facebook page. Connecting to the internet is done via the router. If we sit in a restaurant, it will be a restaurant's router. It might be protected with a password or even a freely open one. We can get the password from our host if it has one. So the router is a device that allows us to connect to the internet.
Once we are connected, we can browse the web; in our case, it's a Facebook login page.
The flow of logging to FB is that we first type in our browser (Chrome, Firefox, IE, Opera, ...) the URL (www.facebook.com). By pressing the enter, our browser sends a message to Facebook to tell it that we want to log in. Afterward, Facebook will return us a corresponding response message. Our browser is capable of reading that message and presenting it to us. In our case, the response message will be a login page where we can put our email and password.
The messages we (our browser) send and receive from FB are called HTTP requests and HTTP responses, or shorter requests and responses. Every message that our browser sends to some internet page is called a request, and every message our browser gets is called a response.
In that communication, we have two entities, the first is us and our browser, and the second is a remote website (FB in our case). Everything that makes a request is called a client, and everything that receives a request and responds with a response is called a server. In our case, we (our browser) are clients, and the Facebook website is a server.
Risks
If we go back to our picture from the above, we can see that every request made by us to the server has to go through the router. And not only the requests from us but all possible requests made by other people in the restaurant (Alice and Bob) have to go through the router first regardless of what website they are visiting.
But how is that dangerous for us?
If anyone of the users in the restaurant is a smart hacker, let's say it's Bob, he can sniff and see everything that we send to the internet. But how is that?
All of our requests need to go through the router; Bob can easily see what we send and what website we visit by being connected to the same router as us. He can see that we want to visit a FB login page, and moreover, he can see our email and password as we have to type them to log in.
The same rules apply if we use a credit card to shop online. The intruder (Bob) can easily see all the details related to our credit card and steal it.
But how can we prevent this? Let's see what we should be doing to stay safe on public wifi.
What to do to stay safe on a public wifi
Since we know that the intruder, in our case Bob, can monitor what we are doing and what data (email and password) we are sending, we need to find a way to prevent this.
One of the most important rules we should stick to is only to visit the websites that start with https. We can see that in our browser where we put a url address. If we type a facebook website in our browser, we will see this: https://www.facebook.com. That s in the https stands for secure.
We should never be visiting the websites without the s like: http://www.some-website.com.
As we said, s stands for secure. That means the data (email and password) are sent encrypted to the website. For example, when we want to log in to FB, we will type our email and password. And before the data are sent, our browser will encrypt them and then send them afterward.
Encryption means converting human-readable text into non-readable data. For example, our email my@email.com might become something like &82kL/d;";9%$82jdll. Such encrypted text our browser sends to the server.
Even though Bob can see what we are sending, he can see only encrypted data and cannot figure out the original information, in our case, email and password. This way, we are much safer on the public wifi.
Fortunately, Facebook and many other websites use https, which means we don't need to worry about this. But still, we should double-check each website we visit whether it's the case or not.
Even though we are safer now, we are still not 100% protected from fraud. The following picture shows why it is that.
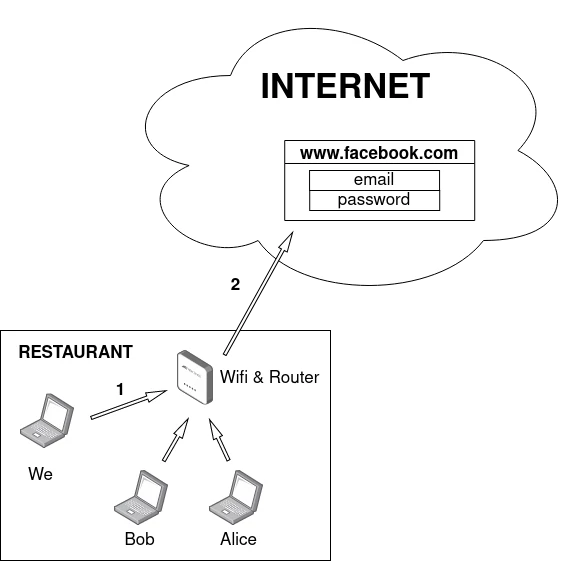
What happens here? As we know, the intruder (Bob) cannot see our email and password anymore, which is fantastic, but he still sees what we are visiting. Since he knows that we are visiting Facebook, he can still harm us.
As we said, all our requests need to go through the router. There, Bob can see that we are visiting Facebook, and he can redirect us to his website. That means we will be redirected to his website instead of Facebook.
We might think, but that's ok; we will see that this is not Facebook but his website. The problem happens if his website looks exactly like Facebook, and we cannot spot a difference. His goal is to visit his website, thinking that we are visiting an actual Facebook website.
To make it look even more convincing, his website url will be very similar to the Facebook url. Let's look carefully at the image above; we will see that the request doesn't go to facebook.com but instead to facebok.com (there is a single o in the name).
He facked not only how his website looks but also the url, which looks very similar to facebook's so that we think we are visiting the real FB. And, of course, because it's his website, he can easily see our credentials (email and password) when we try to log in there.
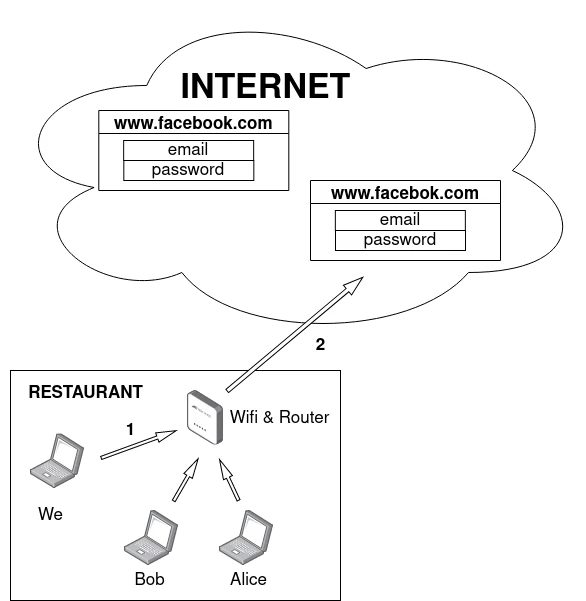
The question is how to prevent this and what we can do about it. The answer is to use a VPN. VPN stands for Virtual Private Network. Let's see what it is.
When we use a VPN, every request we make goes through the VPN first and then to the end destination. In our case, when we visit the FB, the request doesn't go from the router to the FB directly but to the VPN first. Then, the request goes from the VPN to the FB page.
In this case, Bob cannot know what website we visit. He can only see that we are going to the VPN and nothing else. Regardless of what website we visit, the intruders will always see that we are calling the VPN only.
Also, the entire request is fully encrypted, which makes it very difficult for intruders to hack it. They cannot sniff out what we are doing on the internet; thus, they cannot redirect us to their websites.
VPN is just a server that allows us to connect to it and surf the internet with additional safety. There are many VPNs out there, and some of them are even free and very convenient for use.
To use it, all we need to do is find the one (we can search on google), sign up on their website and follow the instructions. Usually, we need to install it on our local computer and run it before going to the internet. And that's all.
Everything else, including sending the requests to VPN first, happens in the background. We, as users, will not even notice that; everything is done automatically, and we don't need to worry about it.
Conclusion
To stay relatively safe on the internet using public wifi, we need to make sure to use a VPN and visit the websites that start with https only.
Relatively safe means that we can never be 100% secure by using public wifi and generally on the internet.